There comes a time when every good admin has the realization that Pre-Shared Keys (PSK’s) are not a great way to manage wireless networks. I once had the pleasure of working on a wireless network when the PKS was changed on the 1st of each month and emailed out to everyone who was “authorized” to be on the network. There were obvious flaws to this approach. WPA2-Enterprise allows users to connect to a wireless network and use their Windows credentials to authenticate. This give us much more control over who we allow onto our networks.
In this blog I’ll go through the setup of NPS (Network Policy Server) on Server 2019 and then I’ll cover how to setup a new SSID using 802.1x auth on Aruba Instant.
Lab setup
I’m going to be doing this from my home lab. Setup is as follows:
- Domain Controller – LAB-DC1 (10.1.1.11)
- NPS Server – LAB-NPS1 (10.1.1.21)
- Aruba Virtual Controller (172.20.10.2)
- 2x Aruba 205 AP’s (172.20.10.101 & 172.20.10.103)
- Lab VLAN ID 101
I have already confirmed connectivity between the AP’s and servers. LAB-DC1 has the Active Directory, DHCP and Certificate Authority roles already installed. LAB-NPS1 has the Network Policy and Access Services role installed. An AD group called ‘Wireless Users’ has been created as well as a couple of test user accounts.
NPS setup
First we need to add our RADIUS client. There are a few options here – we could add each AP individually, we could add range with an IP and netmask if we had a dedicated network for our wireless AP devices, but I like to just add the virtual controller and make sure all authentication requests come from there.
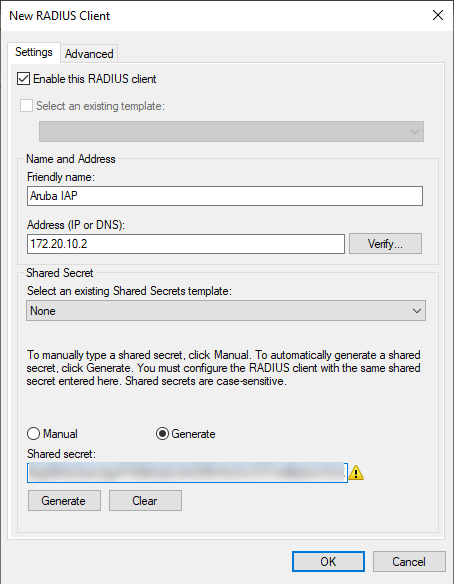
To get started, open the Network Policy Server window, right click on RADIUS Clients and select New. In the New RADIUS client window, enter a Friendly name, the IP address of your virtual controller and either generate or manually enter a shared secret. Take note of this secret key as we’ll need it later on. Click OK when done.
Next we need to setup our Policy. Right click on Network Policies and select New. Give the policy a name and select Next. Now we need to set our conditions. Click Add and select User Groups, then add the ‘Wireless Users’ group. We also want to add NAS Port Type and tick the box for Wireless – IEEE 802.11.

Click Next. Obviously we want to grant access so click Next again without changing Access Permissions.
Now we have to select an EAP type. Click Add and select Microsoft: Protected EAP (PEAP). Now click Edit and make sure you’re using a valid certificate. The Less secure authentication methods can all be unchecked.

Click Next. No other settings need to be changed, so keep clicking Next until the New Policy Wizard finished.
NPS Logging
Unless configured otherwise, your Network Policy Server won’t log successful or failed authentication attempts to event log. This can make troubleshooting quite challenging. To enable logging, launch CMD as Admin and run the following command:
auditpol /set /subcategory:"Network Policy Server" /success:enable /failure:enable
Aruba setup
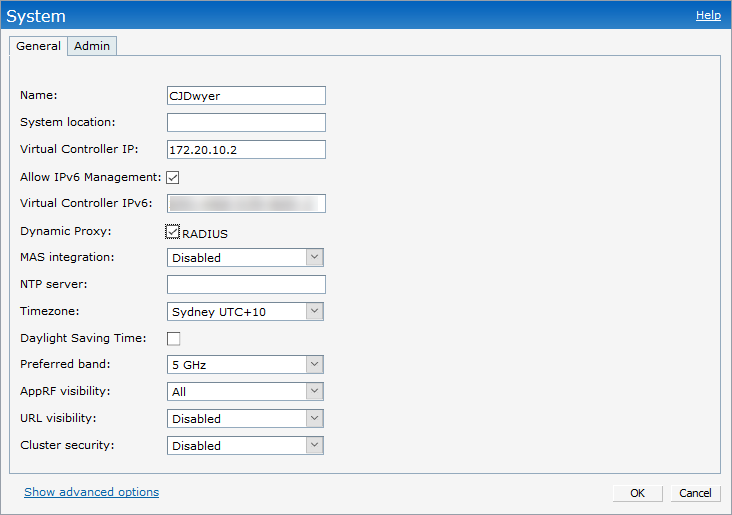
First things first, we need to change a setting so all authentication requests come from the virtual controller than than each individual AP. Open the System menu and check the Dynamic Proxy: RADIUS box. Click OK.
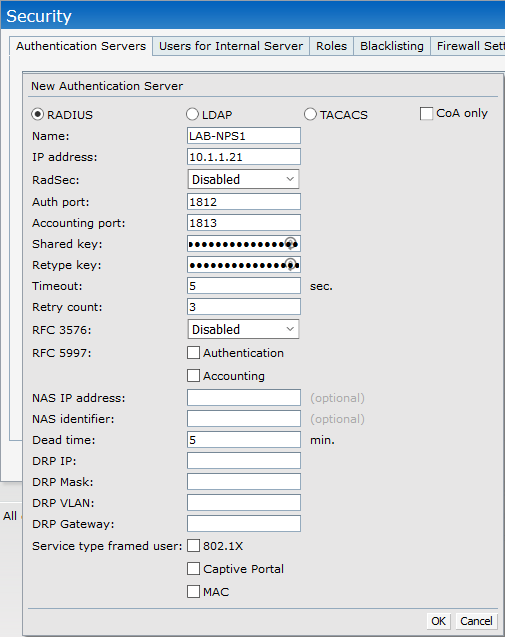
Now open the Security menu and add a new Authentication Server. Enter the name, IP address and Shared Secret from your NPS server. All other settings can stay as default. Click OK and close the security menu.
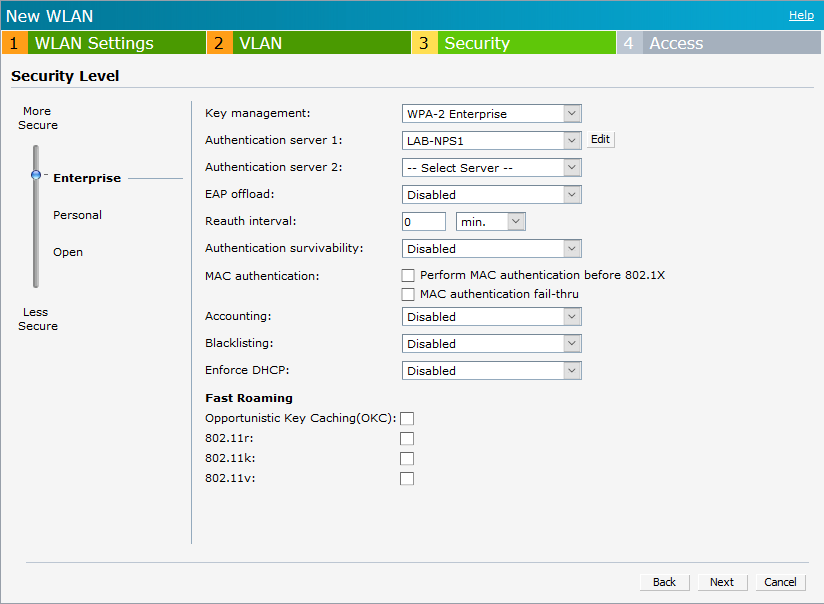
Create a new SSID or edit an existing network. On the security tab, set the security level to Enterprise. Make sure Key Management is set to WPA-2 Enterprise, and select your NPS server from the Authentication Server dropdown menu. Select Next and save your settings.
Connecting to WiFi
Now when users attempt to connect to WiFi they will be prompted for a username and password. Once valid credentials are entered they will be successfully joined to the wireless network. In a future post I’ll look into the use of certificates to remove the need for entering a username and password on domain joined PC’s.

Troubleshooting
If all authentications are failing, the first place you should look is your shared secret. Check and make sure it is the same on both the NPS server and Virtual Controller. I have even see cases where some devices have issues with certain special characters in the shared secret key. To rule this out you can set your shared secret to something super simple for testing and change to something more secure once you have everything working.
Final Thoughts
We’re only just beginning to scratch the surface of what’s possible with 802.1x auth here, but this is a great place to start. Trying to manager PSK’s on wireless networks just doesn’t scale or give you the control over who’s on your networks that you need. Tying wireless access back to AD users makes it much simpler to control who’s on your network, or more importantly, who’s not on your network.
thank you very much it is working fine.
LikeLike
Question, in your example you just added the virtual controller, not the individual AP’s. It looks like the previous admin in my environment did the opposite. I’m about to rebuild a new NPS server and would like to know if I should add just the VC, or both the VC and all the AP’s?
LikeLike
Great question!
Well the answer really depends on your Aruba (or other wireless vendor) setup. Have a look at System settings, and on the General tab you’ll see there’s an option for Dynamic Proxy: RADIUS. When Dynamic RADIUS Proxy is enabled, all your RADIUS authentication requests will come from the master AP (or controller), instead of coming from the Access Point the client is connecting to.
If you dont have this option checked, then each of the AP’s will make their own RADIUS requests back to your NPS server.
Personally, I prefer to use Dynamic RADIUS Proxy as it simplifies management from the NPS side of things. Sure, adding one or two AP’s to NPS isnt too bad, but it becomes a challange to maintain at scale. But having said that, both options are valid and there’s no right or wrong way here.
Good luck wiht your NPS server rebuild!
LikeLike